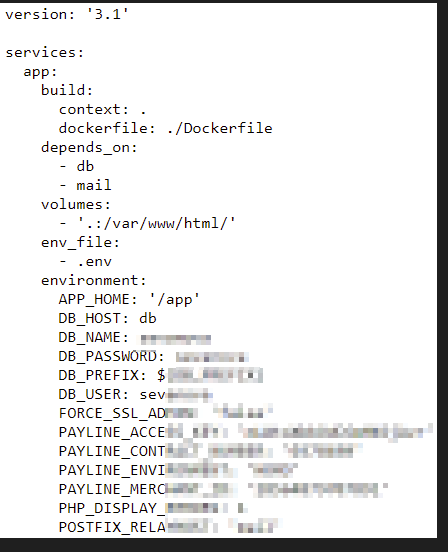
docker-compose.yml exposure
Context
Docker compose is a tool for defining and running Docker applications.
With Compose, developers use a single configuration file (docker-compose.yml) to define and run several application’s services.
Sometimes, developpers push by mistake this file in production environments.
Because this file contains usually all the informations required to deploy an application, it is not uncommun to have passwords and other secrets present in this file.
Exploit or command to run
There is no command or exploit to run, you can access the docker-compose file through the following URL in your favorite web browser:
0/docker-compose.yml
Consequences
By accessing an exposed docker-compose.yml file, an attacker could leverage the vulnerability to gain unauthorized access to sensitive information.
If passwords are found, immediate access to the server can be obtained and even if no secrets are present, important insights about the internals of the application may be reveal allowing therefore a malicious actor to craft a targeted attack.
Remediation
Ensure that the docker-compose.yml file is not deployed with the application or, at least, is not exposed in a web server directory by setting proper permissions on it.
If sensitive information like credentials are leaked in the exposed file, they should be revoked and reset on the affected assets.