directory-listing
Context
A directory listing provides an attacker with the complete index of all the resources located inside of the directory.
The specific risks and consequences vary depending on which files are listed and accessible.
Stoïk only dicloses this vulnerability when impacted files are :
- Source code of the application;
- Usernames, passwords or hashes;
- Personal data of users (bank data, ID's, Curriculum Vitaes)
Exploit or command to run
There is no command to run, access a directory index to list the files.
/wp-content/uploads
Consequences
Exposing the contents of a directory can lead to an attacker gaining access to source code or providing useful information for the attacker to devise exploits, such as creation times of files or any information that may be encoded in file names.
The directory listing may also compromise private or confidential data.
Remediation
Apache
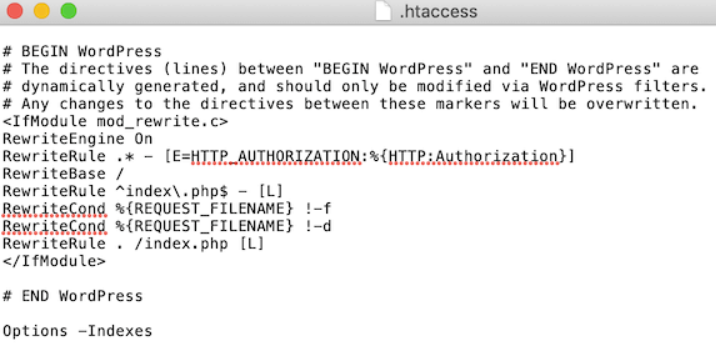
To disable directory listing, you’ll need to add some code to your site’s .htaccess file.
To access the file, you’ll need an FTP client, or you can use the file manager app inside your WordPress hosting control panel.
After connecting to your site, simply open your website’s ‘public’ folder and find the .htaccess file. You can edit the .htaccess file by downloading it to your desktop and then opening it in a text editor like Notepad.
At the very bottom of the file, simply add the following code:
It will look like this:
Once you’re done, save your .htaccess file and upload it back to your server using an FTP client.
Other web servers
You can find more details on this article if your web server differs from Apache:
https://www.invicti.com/blog/web-security/disable-directory-listing-web-servers