CVE-2021-36748
Context
Prestablog plugin used by Prestablog websites is prone to a SQL error injection, in the versions before 1.7.8.
Verify if this finding is a false positive
To ensure the exploitation is possible, we recommend visiting the path:
https://0/modules/ph_simpleblog/config.xml
You will find a file displaying the version:
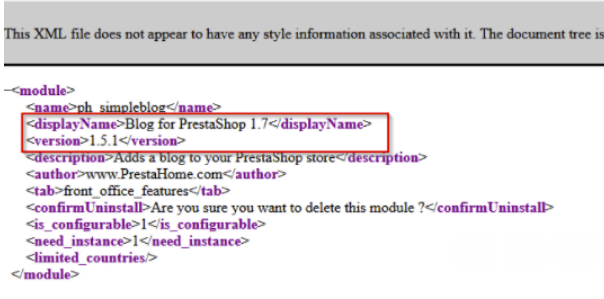
if the version is < 1.7.8, your plugin is vulnerable and your data is at risk.
Impacted Assets
The data contained in the database linked to the Prestashop website.
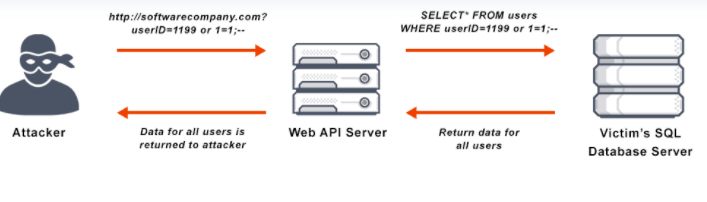
SQL injection is a web attack where user inputs are not sanitized enough and attackers can communicate with the database linked to the website, and access every data stored in the database.
Exploit or command to run
Exploitation can me made through the public tool sqlmap and ran through the following command:
sqlmap -u https://example.com/module/ph_simpleblog/list?sb_category=*
Consequences
Cyber-terms
Direct impact on the confidentiality, integrity ,disponibility and tracability of the assets stored in the database.
Managerial terms
Exploitation of the vulnerability leads to direct financiary losses by impacting confidentiality and integrity of stored data and needed post investigation by security experts to assert cimpacted assets have not been modified.
Remediation
The only remediation is updating the prestablog module to the latest version.