CVE-2021-34473
Context
The vulnerablity named Proxyshell is the combination of 3 differents CVE named :
- CVE-2021-31207 : Access control bypass
- CVE-2021-34523: Privilege escalation on Exchange server backend
- CVE-2021-34473 : Remote Code execution on the server through arbritrary files writing
Consequences
Cyber-terms
An attacker that can interact with the impacted Exchange server can gain local admin privileges on the server.
As Exchange mail server often run with Domain Admin privileges, compromise of the whole Active Directory domain is at risk.
Managerial terms
Exploitation of the vulnerability leads to direct and indirect financiary losses by granting high privileged access on the network to an attacker.
Exploit or command to run
Exploitation can be made through the use of public code.
Searching web browsers leads to publicly accessible code sources like : https://github.com/dmaasland/proxyshell-poc
We can test the first step of the exploit by running the proxyshell_enumerate python script, which will provides us with the list of e-mail adresses of the mail server:
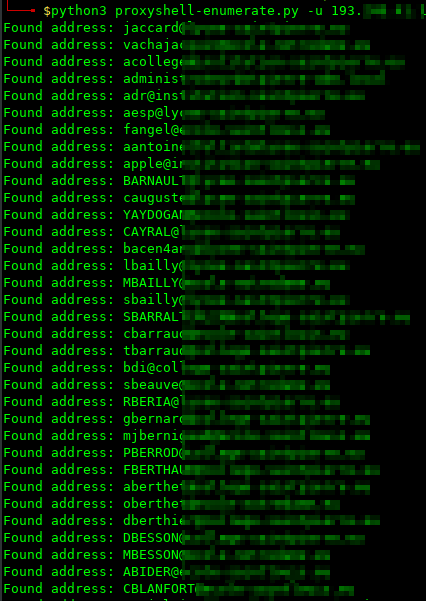
This step proved us the Exchange Server is vulnerable to the exploit and Remote Code execution is also possible.
Remediation
The only way to remediate this vulnerability is by updating the Exchange Server version.
As this vulnerability has been actively exploited, we recommend calling cyber security professionals in order to ensure the network has not been breached.