CVE-2021-22205
Context
On September 21, 2021, Gitlab published a security issue on the handling of images through their internal library Exiftool. The sending of malicious images leads to remote code execution on the server hosting the vulnerable GitLab.
Impacted Assets
The underlying server hosting the GitLab application.
As the vulnerability allows the attacker to take control of the server, the impact can lead to lateral propagation on connected assets depending on security configuration.
Exploit or command to run
Public exploits are released in the Internet. Quick search of the keyword "CVE-2021-22205" leads us to this public Github repository: https://github.com/inspiringz/CVE-2021-22205.
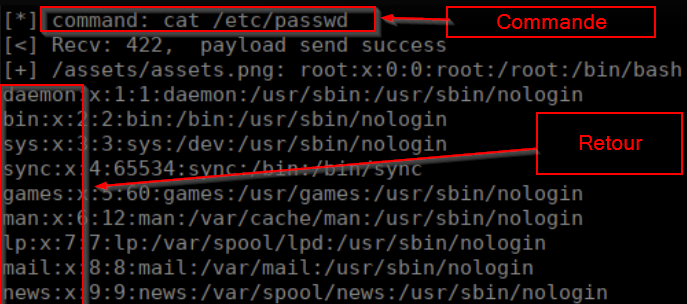
From then, use of the proof of concept is trivial and allows the execution of commands, as in the example below listing the content of the server directory:
Consequences
Cyber-terms
Direct impact on the confidentiality, integrity ,disponibility and tracability of the assets stored in the server. As the exploitation of the vulnerability does not need authentication to the platform or the server, its impact is critical and grants shell access to the attacker.
Managerial terms
Exploitation of the vulnerability leads to direct financiary losses by impacting security of business assets and needed post investigation by security experts to assert the underlying network has not been compromized.
Remediation
Short-term action
Restriction access needs to be immediately deployed to restrict the access of GitLab server to exclusively known developpers.
As such, GitLab is an intern service and should not be accessed from Internet.
This can be done by restrict features of the server such as configuration of .htaccess files for Apache servers or creation filtering rules in the case a firewall is protecting the server.
Mid term Actions
As the short-term actions cannot be effective in the long term and will induce complexity and human work, the only remediation possible is to upgrade GitLab version to the latest running version (Gitlab version 14.7.8 at the date of this document redaction) :