subdomain-takeover
- Github
- Shopify
- Netlify
- Wix
- AWS S3 bucket
- The victim’s external DNS server subdomain record is configured to point to a non-existing or non-active resource/external service/endpoint. The proliferation of XaaS (Anything as a Service) products and public cloud services offer a lot of potential targets to consider.
- The service provider hosting the resource/external service/endpoint does not handle subdomain ownership verification properly.
If the subdomain takeover is successful, a wide variety of attacks are possible (serving malicious content, phishing, stealing user session cookies, credentials, etc.). This vulnerability could be exploited for a wide variety of DNS resource records including: A, CNAME, MX, NS, TXT etc.
In terms of the attack severity an NS subdomain takeover (although less likely) has the highest impact because a successful attack could result in full control over the whole DNS zone and the victim’s domain.
We are gonna walk through a Shopify domain takeover for this example but the same scenario can be applied for the other applications.
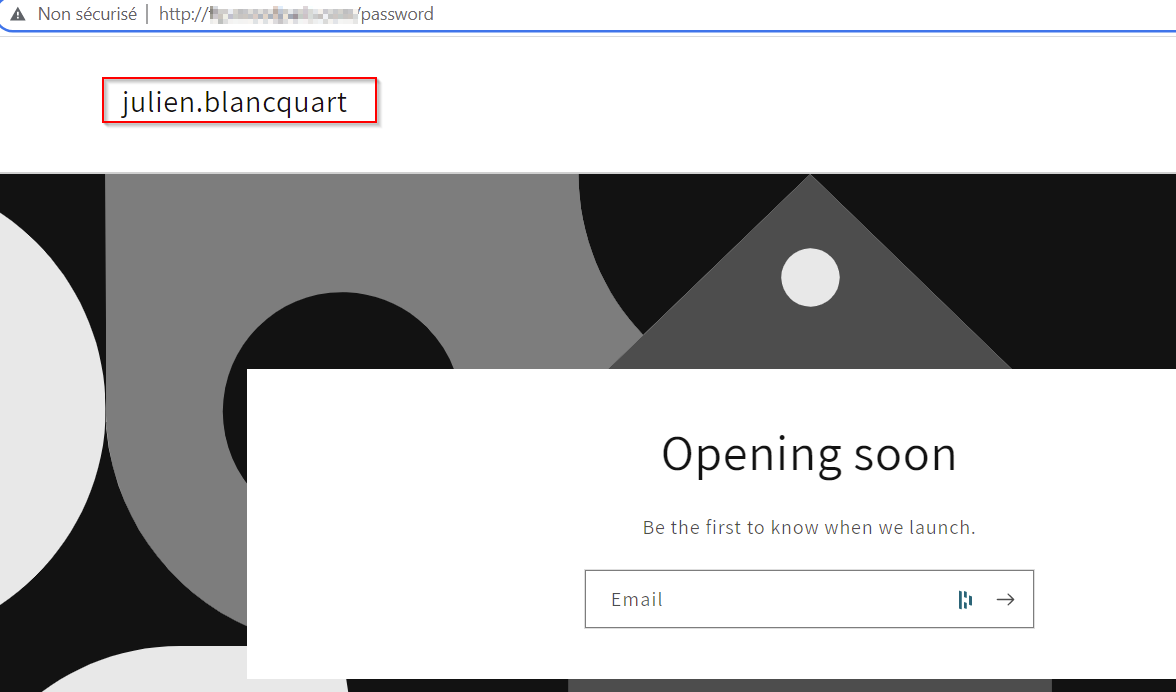
When arriving to the vulnerable subdomain, we are greeted with the following:
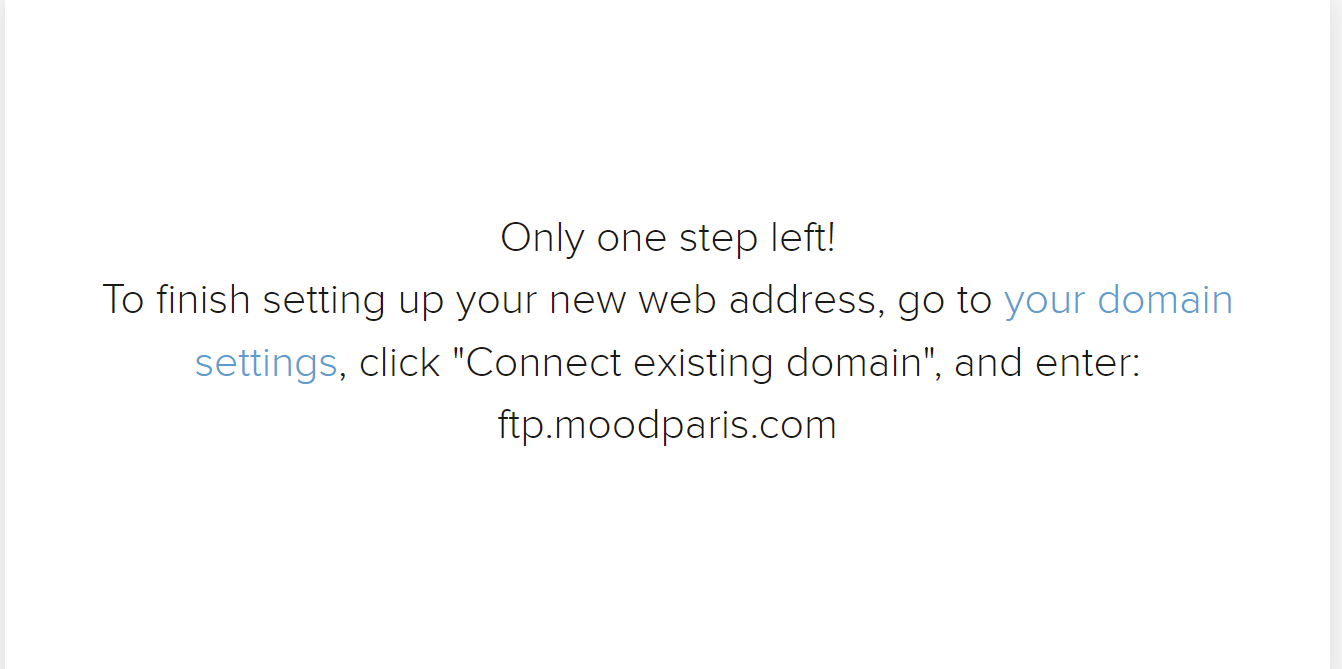
Then, we can simply connect the available domain in the shopify admin panel:
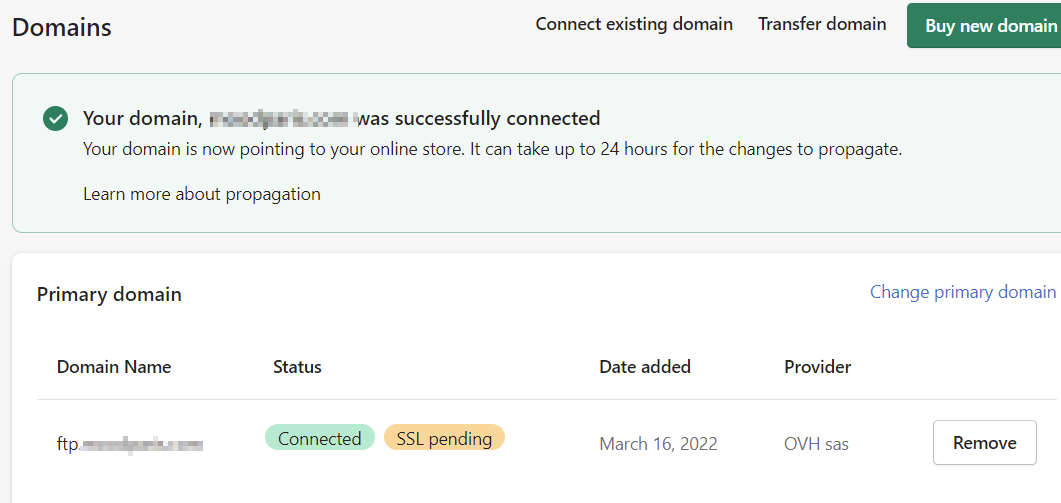
Then our own website is accessible through the subdomain impacted: